Title
Create new category
Edit page index title
Edit category
Edit link
JWT
JWT, or JSON Web Token, is an open standard to securely transmit data between parties as a JSON object. We use JWT in the Lightbits SDS for all API calls (lbcli and REST/GRPC). By default, the cluster will be created with a system JWT (Cluster Admin) and a default JWT that is associated with the default project Admin (can only do project level APIs on the default project). If you create more projects/tenants, you will have additional Admin JWTs for each project.
The JWT is stored in a Keyvault created in the managed resource group during deployment.
Get the System JWT from Azure Portal
- Log in to the Azure portal.
- Click the managed application that you created (it should be in the resource group that was defined during the deployment).
- Click the managed resource.
- You will see a list of all of the resources created for the cluster.
- Click the Keyvault.
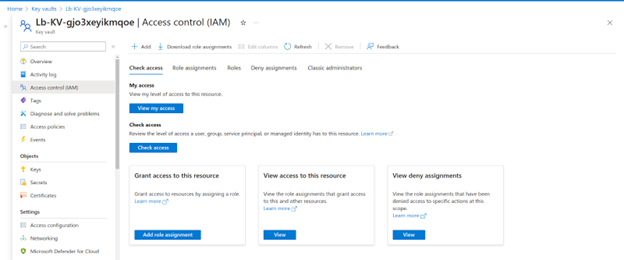
- Go to the Access Control menu.
- Click Add Role Assignment.
- Select the Key Vault Secrets User role.
- Click Next.
- Click Add Member.
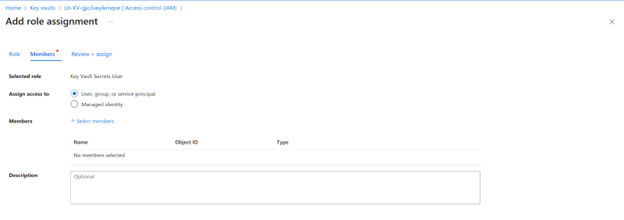
- Choose the user that will be able to read the JWT.
- Click Review and Assign.
- Go to the Secrets menu in the Keyvault.
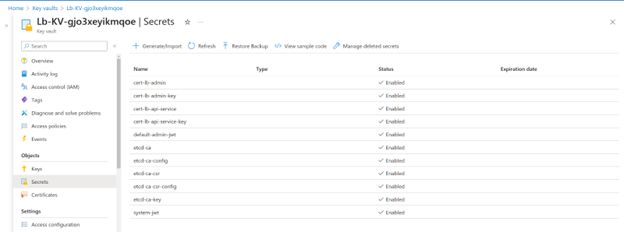
- Click the system JWT or the Admin JWT of the default Project.
- Click the current version of the secret.
- Click Show Secret.
- Copy the secret value.
Get the System JWT from Azure CLI
You can also do this using Azure CLI.
- List all keyvaults in the subscription:
az keyvault list
- Select the relevant keyvault name and list all the secrets:
az keyvault secret list --vault-name <kv_name>
- Select the relevant Secret to show:
az keyvault secret show --vault-name <kv_name> --name <secret_name>
Once you have the JWT, it should be used in every lbcli or API call to the Lightbits cluster. For use in this document and examples, we refer to an environment variable called: $LIGHTOS_JWT
For example:
lbcli list nodes -J $LIGHTOS_JWT
What to Do with the JWT
It is recommended to save the system_jwt as an environment variable, so that it can be easily added to any lbcli or API command.
For example:
lbcli list nodes -J $LIGHTOS_JWT
You can also save the JWT in the lbcli configuration YAML file /etc/lbcli/lbcli.yaml. This allows you to perform additional lbcli management commands to the storage cluster without specifying the JWT in each command.
For example:
lbcli list nodes -J $LIGHTOS_JWTName UUID State NVMe endpoint Failure domains Local rebuild progresslbcluster_0001 1c221509-be0c-57f9-9f66-980174d8f91a Active 10.240.99.56:4420 [i-020acc69e738c6c39 ip-1...] Nonelbcluster_0002 83bb07d7-2bb8-5e8e-a3db-fce76288b971 Active 10.240.99.224:4420 [i-04896c6c251c859b1 ip-1...] Nonelbcluster_0003 ad122562-be10-5268-82d0-7fa41349f9f7 Active 10.240.99.148:4420 [i-017209734ebc14b03 ip-1...] None> vi /etc/lbcli/lbcli.yamloutput-format: human-readable dial-timeout: 5s command-timeout: 60s insecure-skip-tls-verify: true debug: false api-version: 2 insecure-transport: false endpoint: https://127.0.0.1:443 jwt: <the JWT you copied>Once you have the JWT, you can start working on the lbcli or Lightbits APIs to create volumes and start mounting them on your clients.
© 2026 Lightbits Labs™